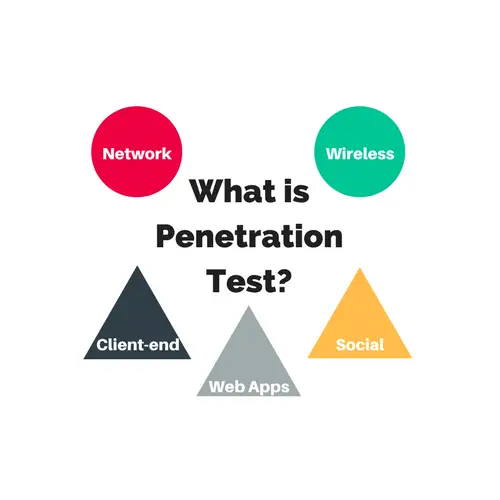
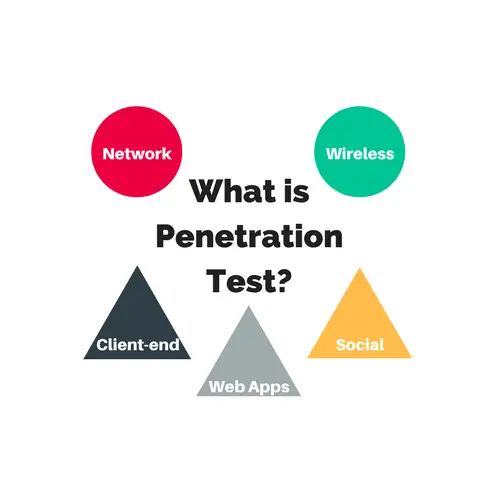
A penetration test, also known as a pen test, is like a planned pretend attack on a computer or device. It helps find problems with security that could put your information at risk. In this article, we’ll talk about different kinds of pen tests so you can plan and do them well.
The extent of a penetration test, like how much you explore a system, depends on what you want to find out. So, a security tester needs to carefully think and choose the right kind of test. That’s why it’s important for a good tester to know about the various types of pen tests.
As a matter of fact, penetration tests are divided into five categories. Click on each one to learn how to plan your tests properly.
Also Read: Pen Testing Concept Explained In-Depth
Network Penetration Test
A network test is the most basic test requirement for pen testers. Its goal is to identify weaknesses and potential data leaks within the client’s network infrastructure. To ensure that the network is secure and doesn’t have any gaps, it is critical to run tests from both the internal and the outside world.
The testers should target the following end-points in their penetration tests.
- Testing firewall setting if exists.
- Perform stateful analysis.
- Firewall evasion testing.
- IPS spoofing.
- Attacks at the DNS level, encompassing:
- Testing for zone transfers.
- Assessing routing-based vulnerabilities.
- Miscellaneous testing of various network parameters.
Also, there is a set of software modules that the penetration test should cover are as follows.
- Testing SSH for clients and servers.
- Databases like MYSQL and SQL Server on the network.
- Email servers like Exchange and SMTP.
- Checking FTP for clients and servers.
Web Applications Pen Test
It is more of a targeted test, also, more intense and detailed. Areas like web applications, internet browsers having ActiveX, Applets, Plug-ins, and Scriptlets fall in the scope of web-based pen testing.
Since this test examines the endpoints of each web app that a user might have to interact with on a regular basis, it needs thorough planning and time investment.
Also, with the increase in threats coming from web applications, the ways to test them are continuously evolving.
Client-Side Pen Test
These tests aim to find security issues that occur within a particular area. For instance, there might be an issue with a software application on a user’s computer that a hacker could exploit.
These may be programs or applications like Putty, Git clients, Sniffers, browsers (Chrome, Firefox, Safari, IE, Opera), and even presentation as well as content creation packages like MS PowerPoint, Adobe Page Maker, Photoshop, and media players.
In addition to third-party software, threats could be homegrown. Using uncertified OSS (open-source software) to create or extend homemade applications could cause severe threats that one can’t even anticipate. Therefore, these locally developed tools should also pass through the penetration test cycle.
WiFi-based Penetration Test
The purpose of this test is to inspect the devices connected using wifi on the client site. These could be portable hardware such as a laptop, mobile phone, iPad, tablet, etc. Apart from the gadgets, the penetration tester should also plan to cover the below items.
- The network protocol these Wi-Fi appliances use to isolate any security holes.
- Wireless access point monitoring for detecting devices that violate access policies
Usually, such tests should take place at the customer end. The hardware used to run pen tests needs to connect with the wireless system to expose vulnerability.
Human-Centric Pen Test
These tests are a type of penetration test that observes the human element of security. These tests simulate attacks that employees might fall for, such as phishing emails or dumpster diving. There are two main types:
- Remote Assessments: These involve tricking employees into revealing sensitive information electronically, often through phishing emails or phone calls.
- Physical Assessments: This requires direct interaction with employees to get sensitive information, using methods like going through the trash, impersonation, intimidation, or convincing someone over the phone.
Please note that you must inform the appropriate people before conducting the social engineering penetration test. Also, remember to emulate real-world exploits instead of playing a movie scene.
Conclusion
We learned a penetration test not only helps in discovering the actual and exploitable security threats but also provides their mitigation.
By performing a pen test, we can make sure to identify the vulnerabilities that are critical, which are not significant, and which are false positives.
We hope that you now know the potential areas to begin designing the perfect penetration tests.
Happy Pen Testing,
TechBeamers